analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
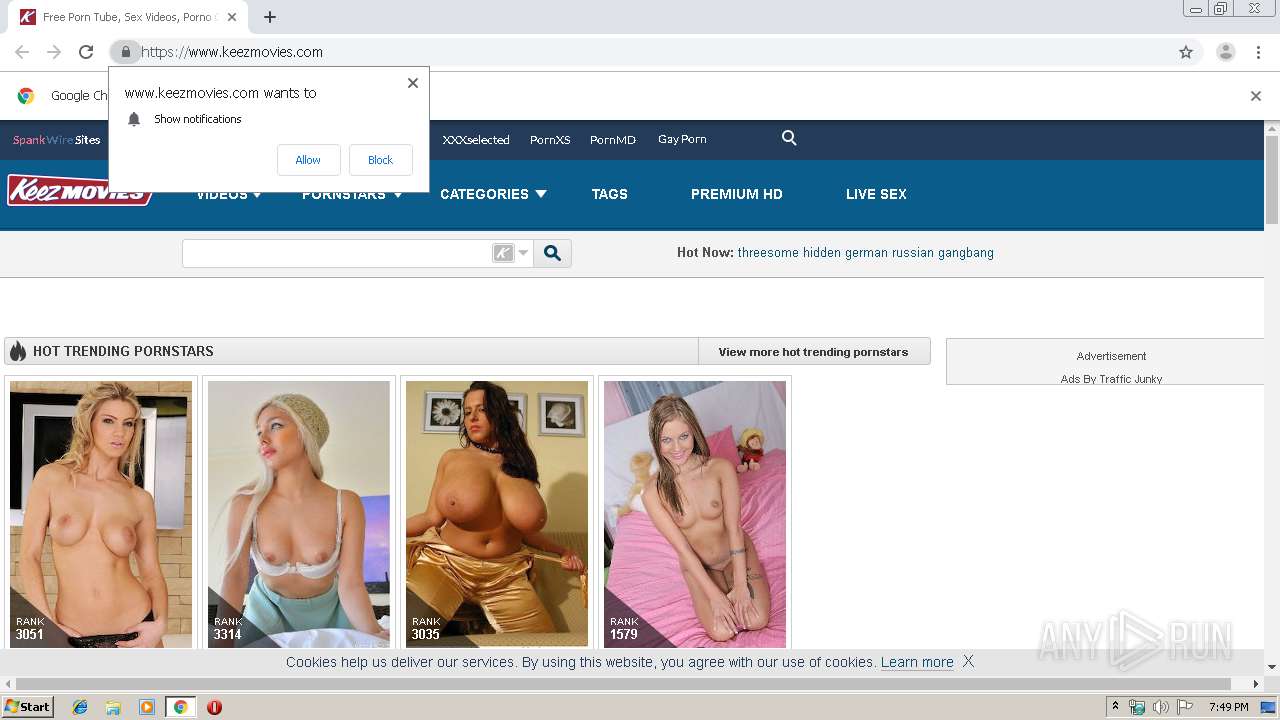
| URL: | http://www.keezmovies.com/ |
| Full analysis: | https://app.any.run/tasks/b162636d-5ecc-4f3e-a59d-cdd981d473b4 |
| Verdict: | Malicious activity |
| Analysis date: | August 23, 2019, 18:49:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A0CA9FCFEF496271C748D455F47F01C7 |
| SHA1: | 6647D42447DF4B0356F09D4839B6CB86D0A86057 |
| SHA256: | 01077BFB1D92620E4133B2240FAD51F7A47AA87C08F9EA59C538113FCE139B2C |
| SSDEEP: | 3:N1KJS4bIgyG:Cc41t |
ANY.RUN is an interactive service which provides full access to the guest system. Information in this report could be distorted by user actions and is provided for user acknowledgement as it is. ANY.RUN does not guarantee maliciousness or safety of the content.
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3556)
INFO
Application launched itself
- chrome.exe (PID: 3556)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
All screenshots are available in the full report
Total processes
55
Monitored processes
21
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.keezmovies.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fd9a9d0,0x6fd9a9e0,0x6fd9a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3416 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3560 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6660624486099013222 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2958089555592867615 --mojo-platform-channel-handle=1620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7520553112818042495 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 3688 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4438276969990550679 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2204 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 4036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=795741158653368133 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2528 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
| 3180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6316676049323806964 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3256 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 75.0.3770.100 | ||||
| 2732 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,13772133699621992432,5168395197555412328,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5282608465887870999 --mojo-platform-channel-handle=3460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 | ||||
Total events
198
Read events
136
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
45
Text files
174
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\841ebeea-b879-4639-8e64-032dfd158f75.tmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:DC32343F45B01764B6267AD36548102A | SHA256:A250F5AD57D4BD58AAE92810D50278E3BE2DBF869F126A3A3519691BCDFC2075 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c25.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169c35.TMP | text | |
MD5:213AE3DA120D7862D60B5763B6C9D466 | SHA256:5736534D6EE654C1BF1A8E79E73330AF58F622E8657285330D2C7189A55604F4 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF169c93.TMP | text | |
MD5:3D551B6E929CF62F7AA66091E718704B | SHA256:1698A1B1BC3E86676392FB8BD4C712438302A5A2220503C08F290ED4B1790404 | |||
| 3556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169c64.TMP | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
54
DNS requests
53
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2076 | chrome.exe | GET | 301 | 31.192.116.179:80 | http://www.keezmovies.com/ | NL | — | — | unknown |
2076 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2076 | chrome.exe | GET | 200 | 173.194.151.233:80 | http://r3---sn-4g5edn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=82.102.26.200&mm=28&mn=sn-4g5edn7s&ms=nvh&mt=1566586098&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | chrome.exe | 172.217.18.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2076 | chrome.exe | 31.192.116.179:80 | www.keezmovies.com | Viking Host B.V. | NL | unknown |
2076 | chrome.exe | 66.254.122.104:443 | cdn1-static-keezmovies.spankcdn.net | Reflected Networks, Inc. | US | suspicious |
2076 | chrome.exe | 31.192.116.179:443 | www.keezmovies.com | Viking Host B.V. | NL | unknown |
2076 | chrome.exe | 172.217.18.110:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2076 | chrome.exe | 94.31.29.128:443 | cdn1.traffichaus.com | netDNA | GB | malicious |
2076 | chrome.exe | 66.254.122.100:443 | cdn1-static-keezmovies.spankcdn.net | Reflected Networks, Inc. | US | suspicious |
— | — | 66.254.122.104:443 | cdn1-static-keezmovies.spankcdn.net | Reflected Networks, Inc. | US | suspicious |
2076 | chrome.exe | 216.58.206.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2076 | chrome.exe | 172.217.16.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.keezmovies.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn1-static-keezmovies.spankcdn.net |
| suspicious |
fonts.googleapis.com |
| whitelisted |
ads2.contentabc.com |
| whitelisted |
cdn.engine.phn.doublepimp.com |
| unknown |
ads.trafficjunky.net |
| whitelisted |
cdn1-download-keezmovies.spankcdn.net |
| unknown |
www.google.com |
| whitelisted |