analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
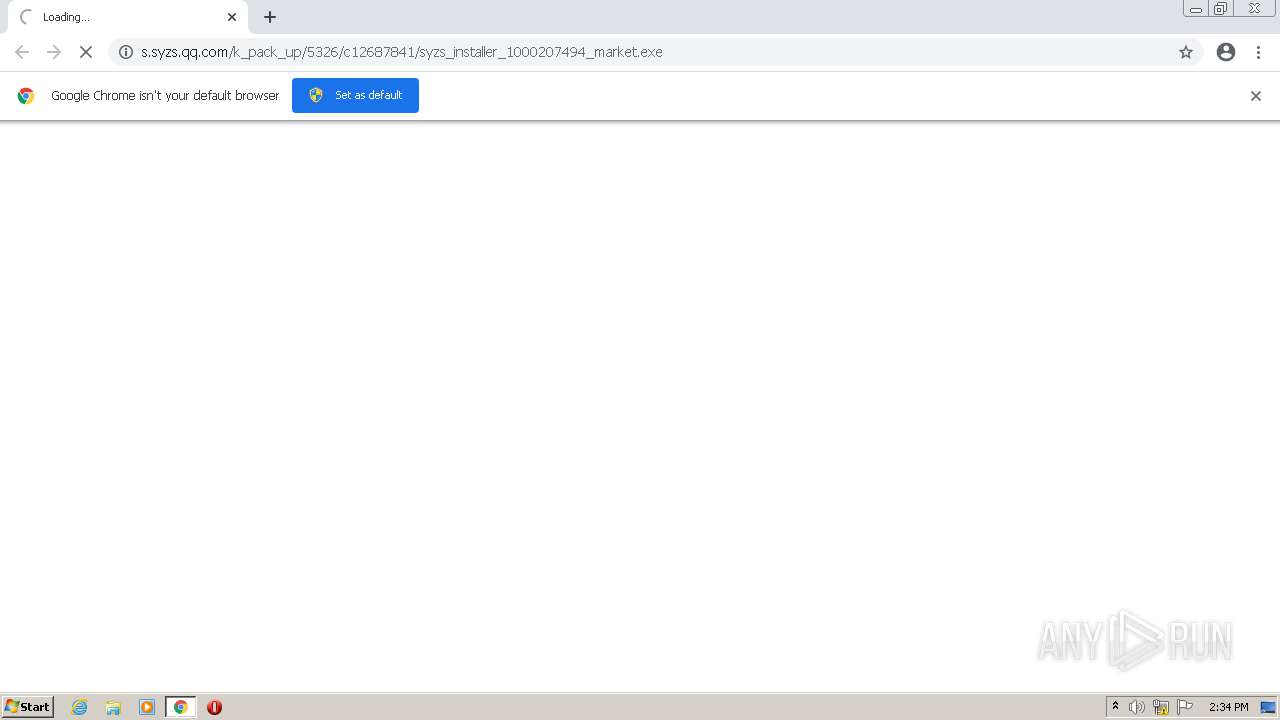
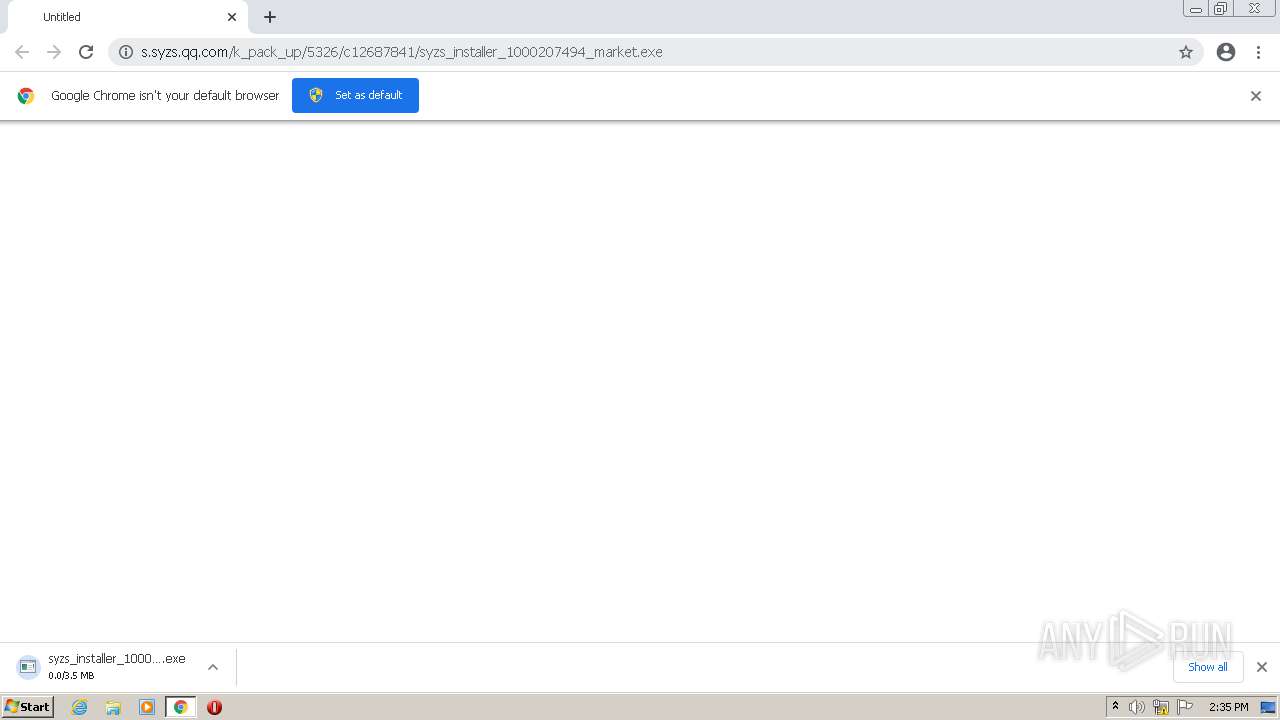
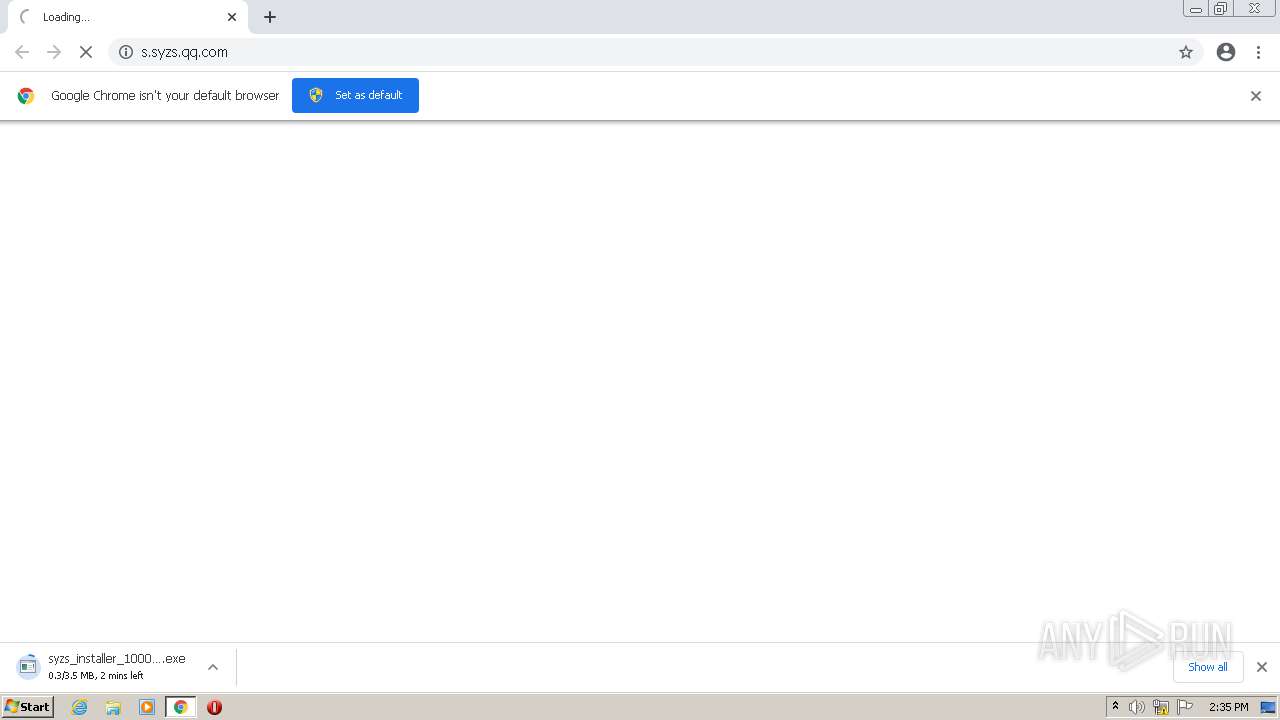
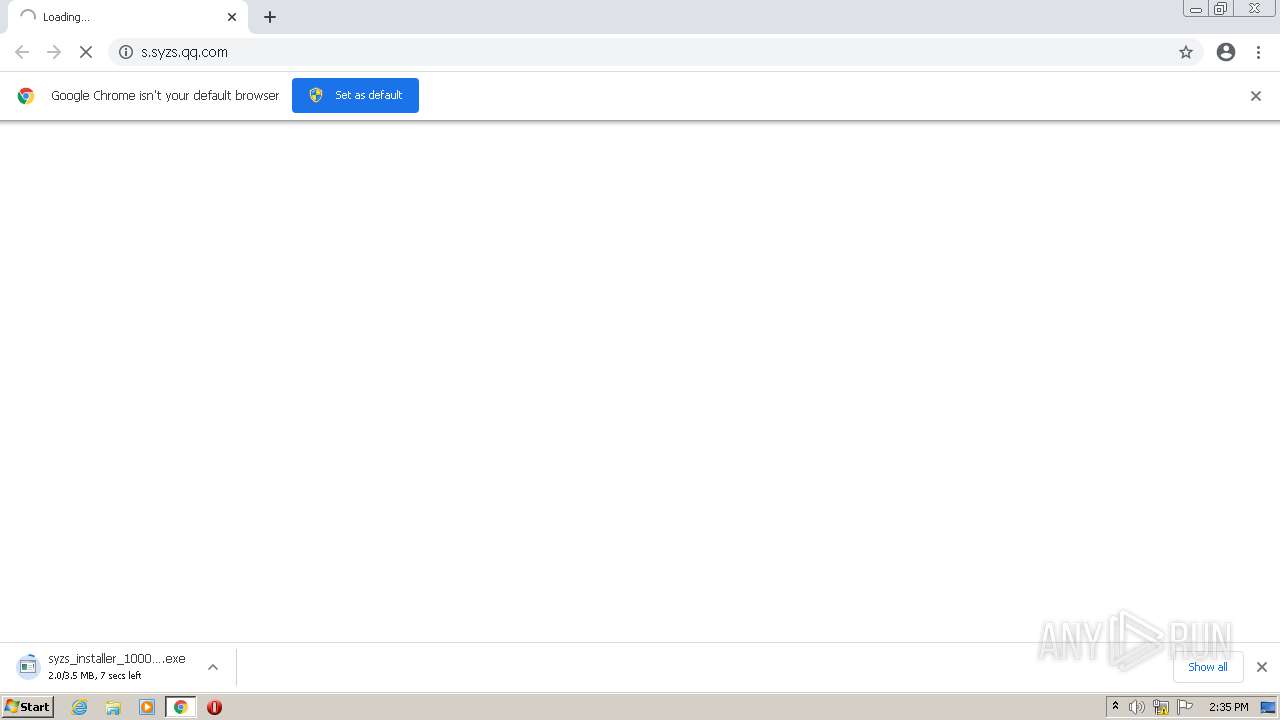
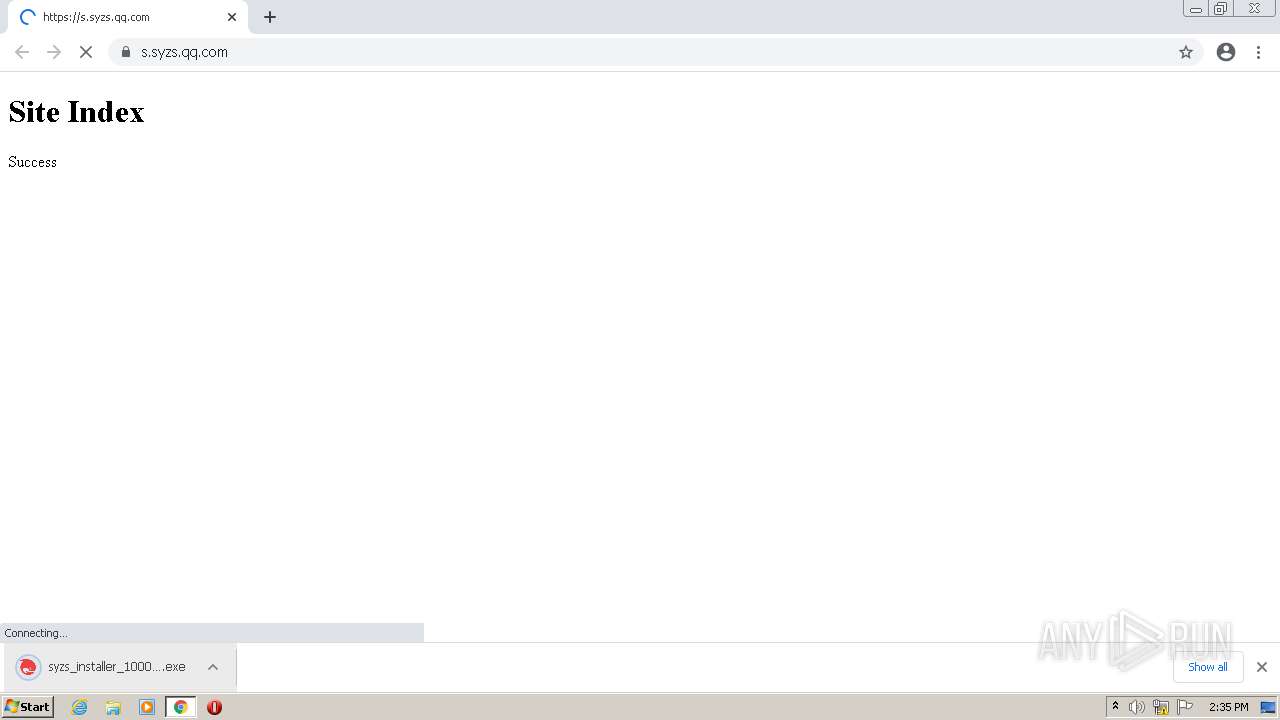
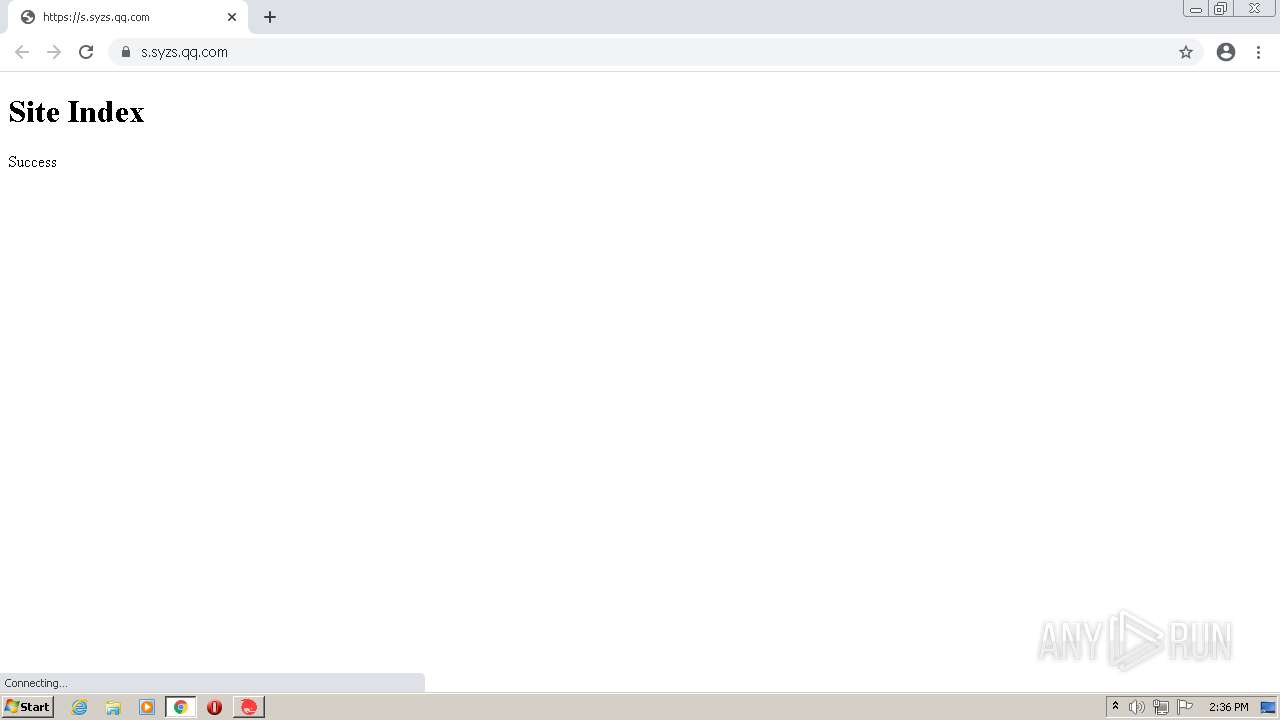
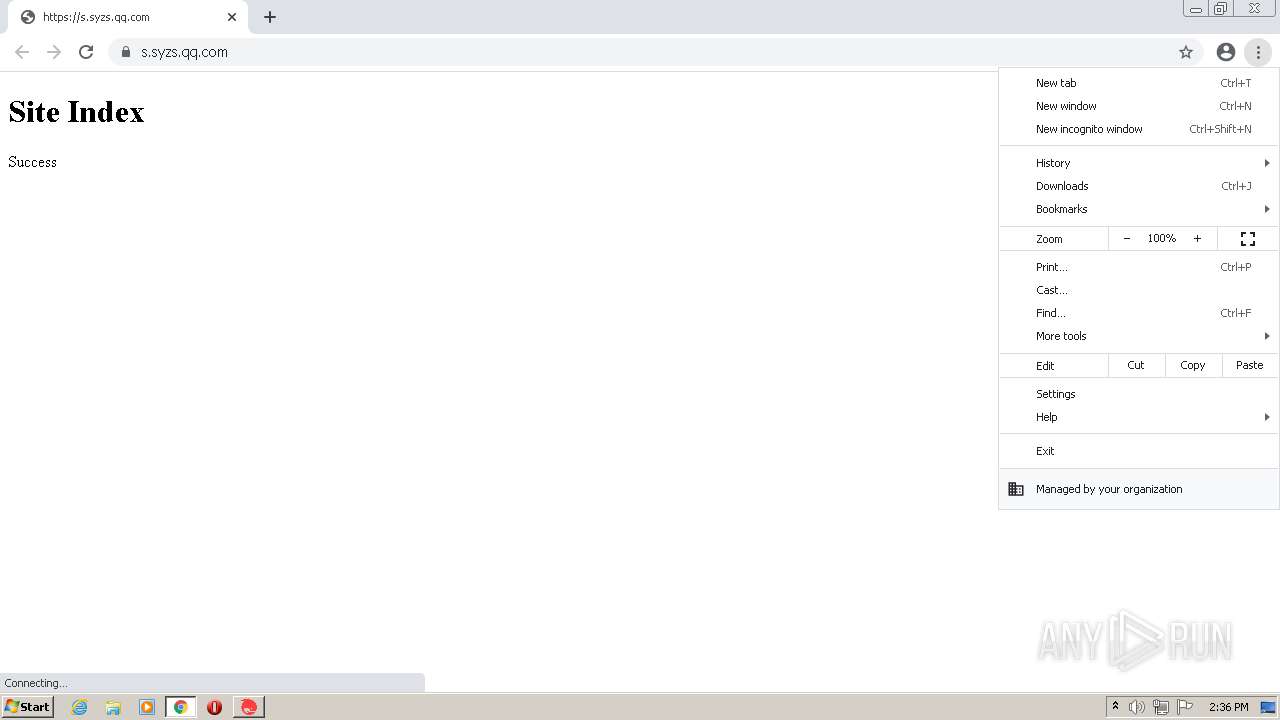
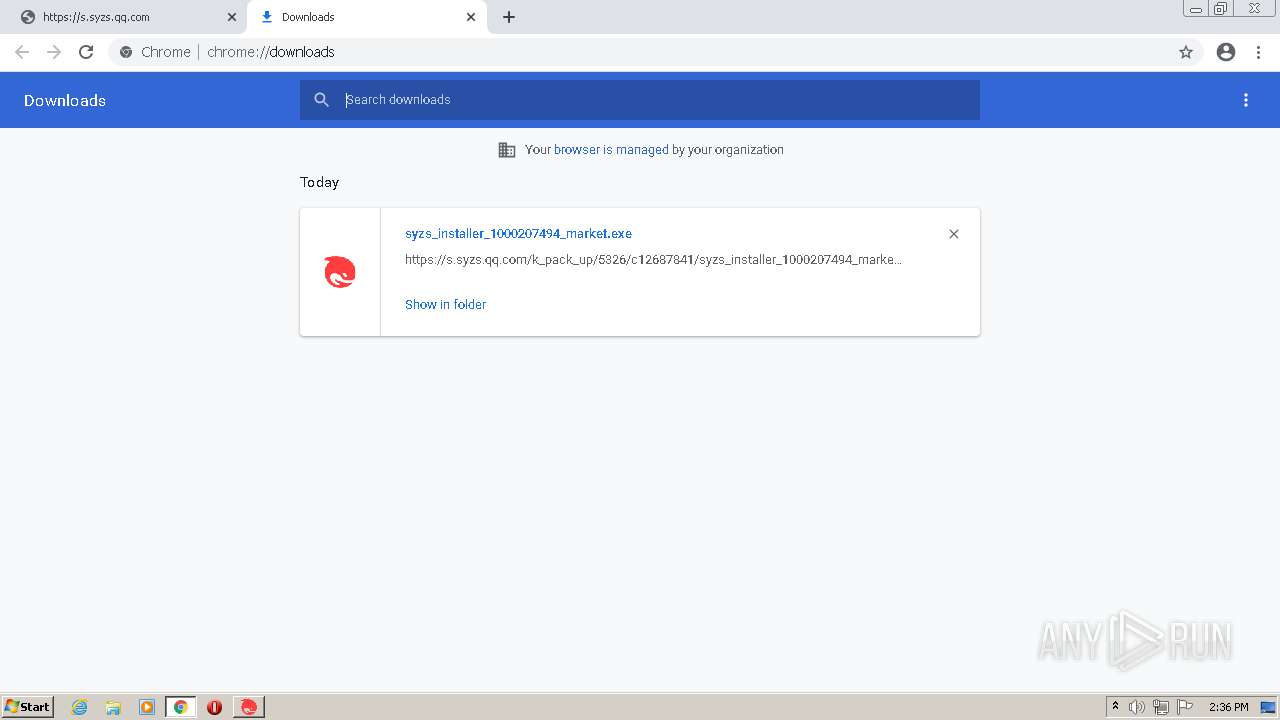
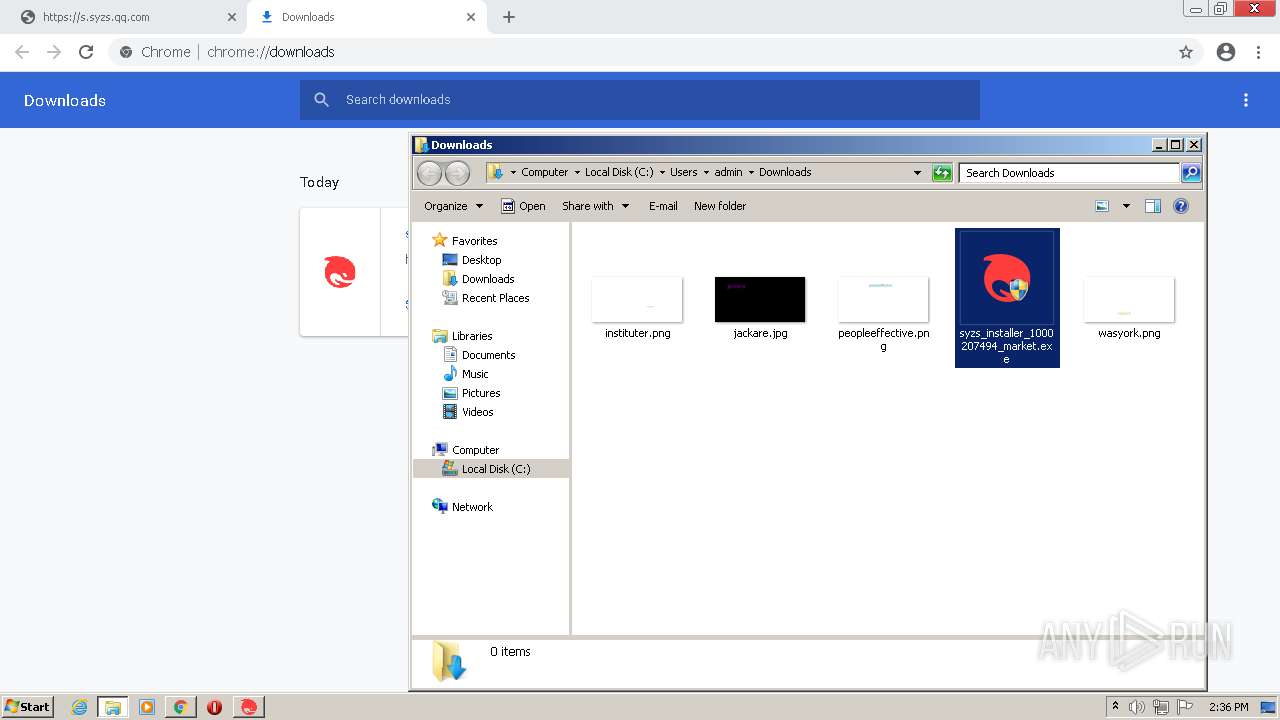
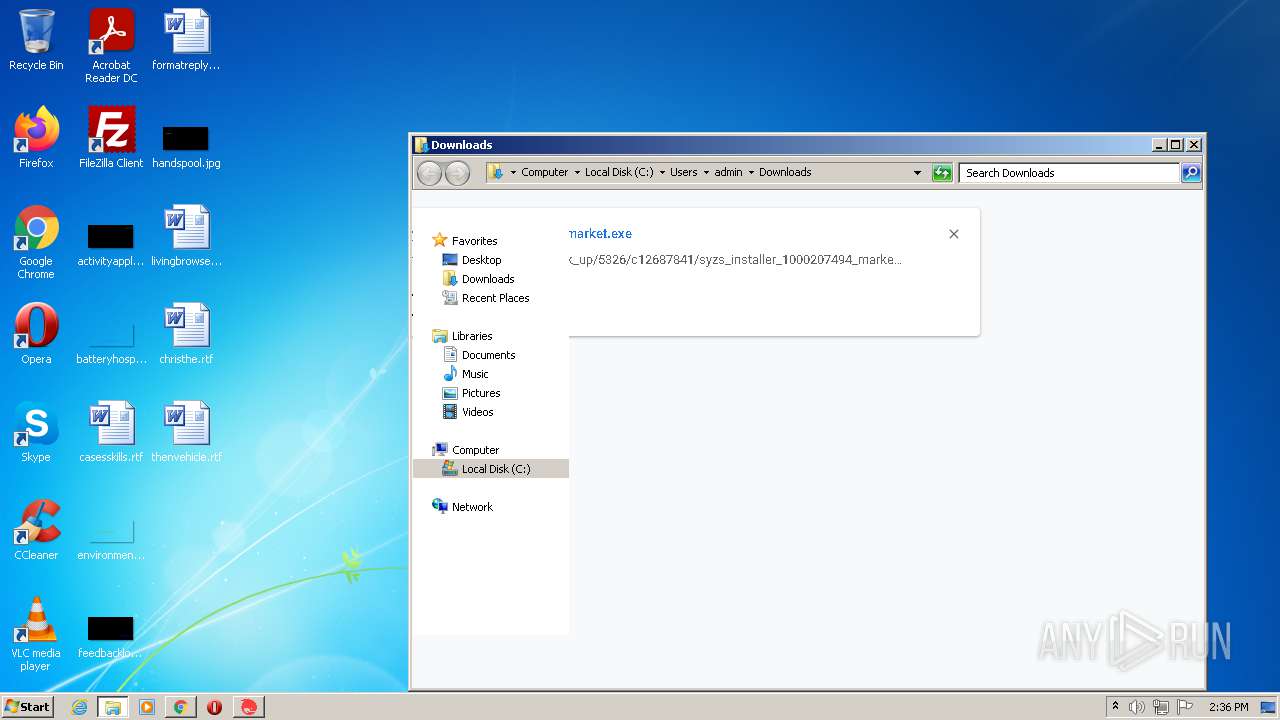
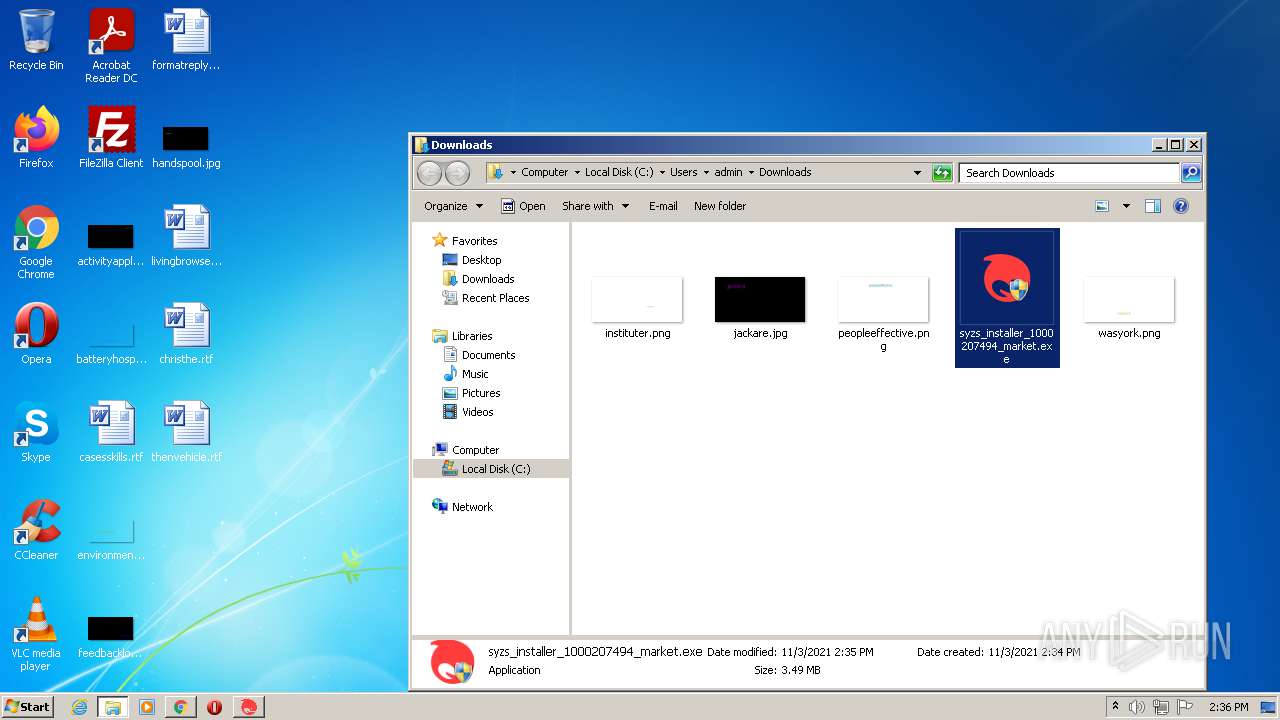
| URL: | https://s.syzs.qq.com/k_pack_up/5326/c12687841/syzs_installer_1000207494_market.exe |
| Full analysis: | https://app.any.run/tasks/a1a95a2d-a14c-446b-8620-8c2953865209 |
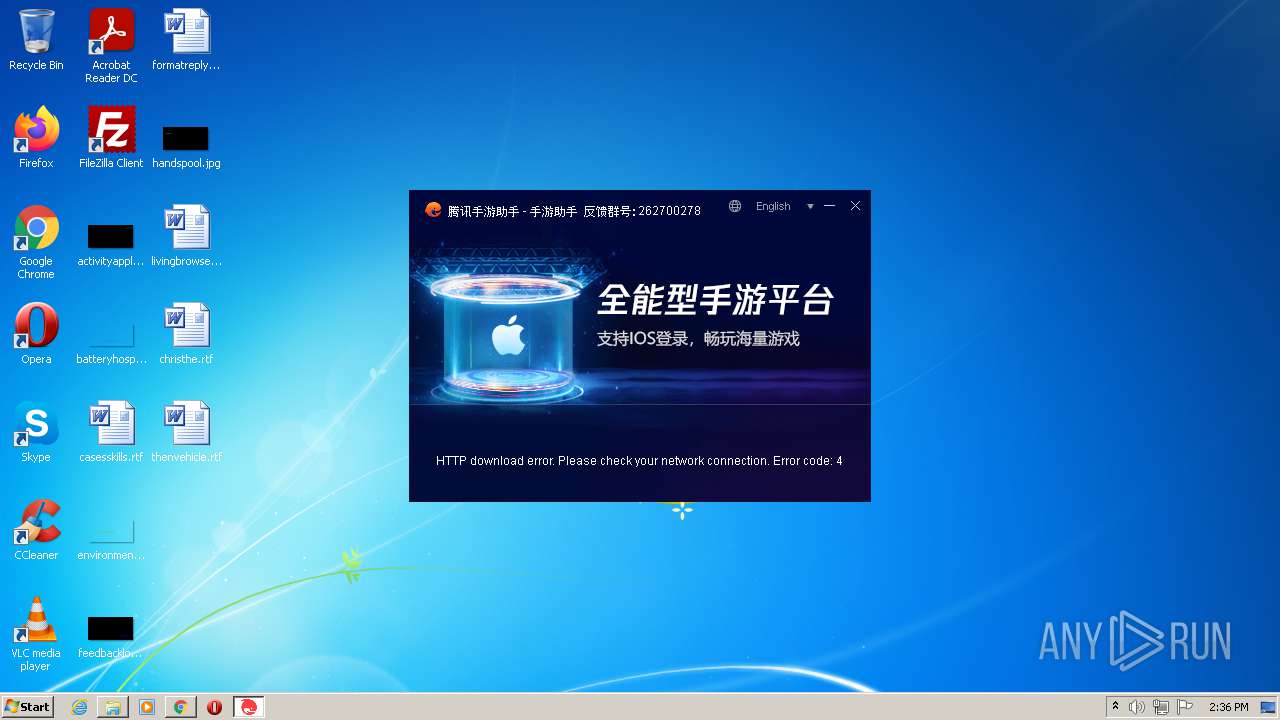
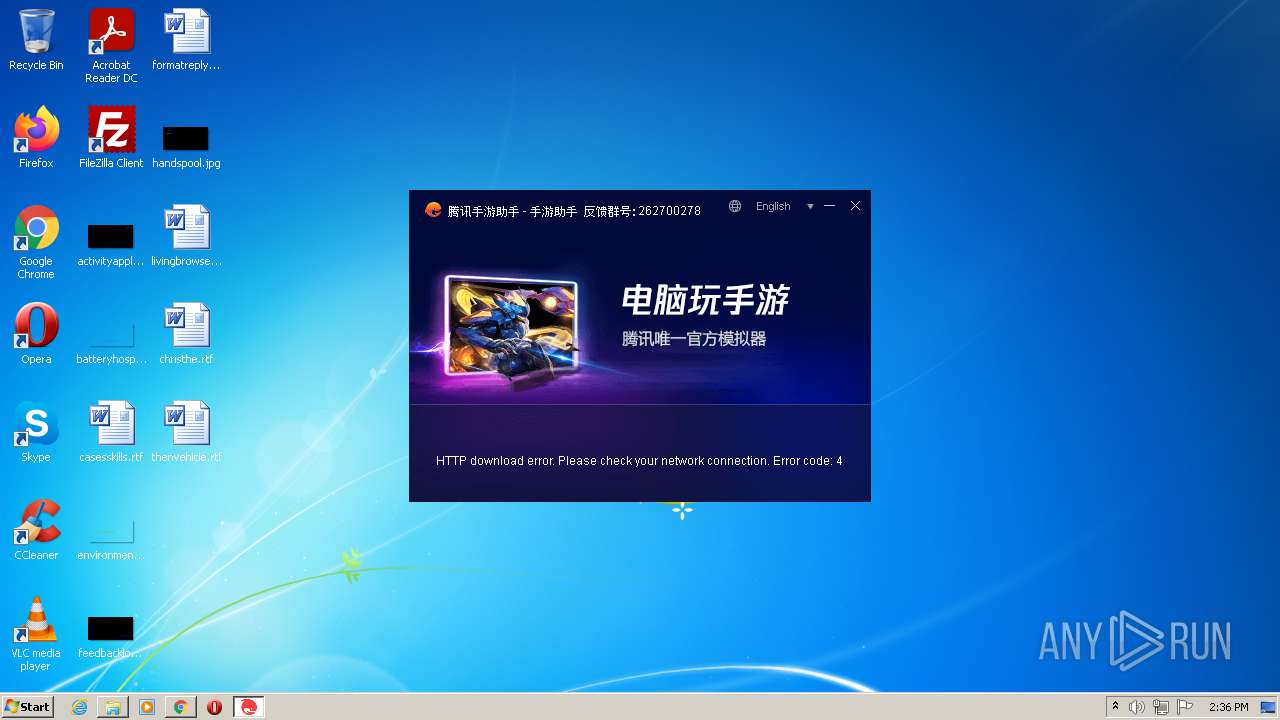
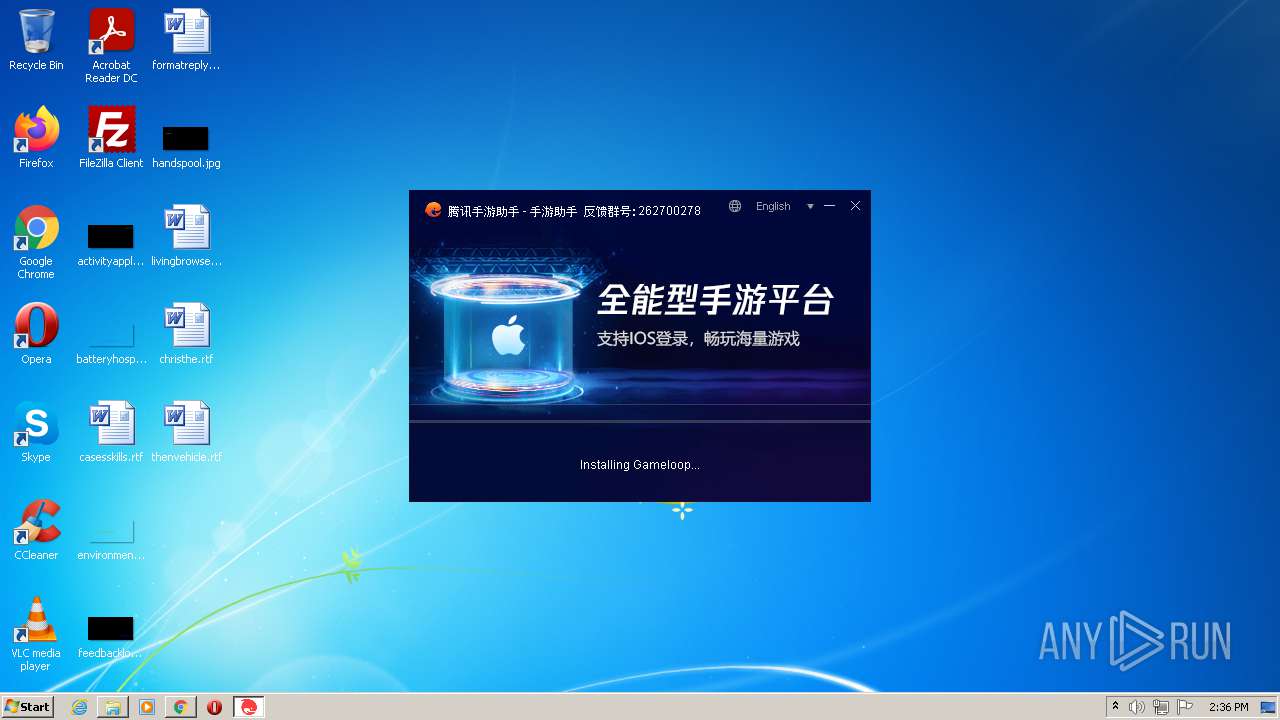
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2021, 14:34:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E92000CDC0BF809BAECE0D392FEB0DFF |
| SHA1: | 34286DC16E8F1D2CFE167A28CFF4EA328C6BFCC3 |
| SHA256: | 690DA1BDD022CDE8EA3330493CF1B82B01F5E360C5EDF48F57735C9C697717D8 |
| SSDEEP: | 3:N8qfMUU8rWXTKG8QnbfWiqOXdVU5eAOA:2aCXTKG8w+ZOXd+F |
ANY.RUN is an interactive service which provides full access to the guest system. Information in this report could be distorted by user actions and is provided for user acknowledgement as it is. ANY.RUN does not guarantee maliciousness or safety of the content.
MALICIOUS
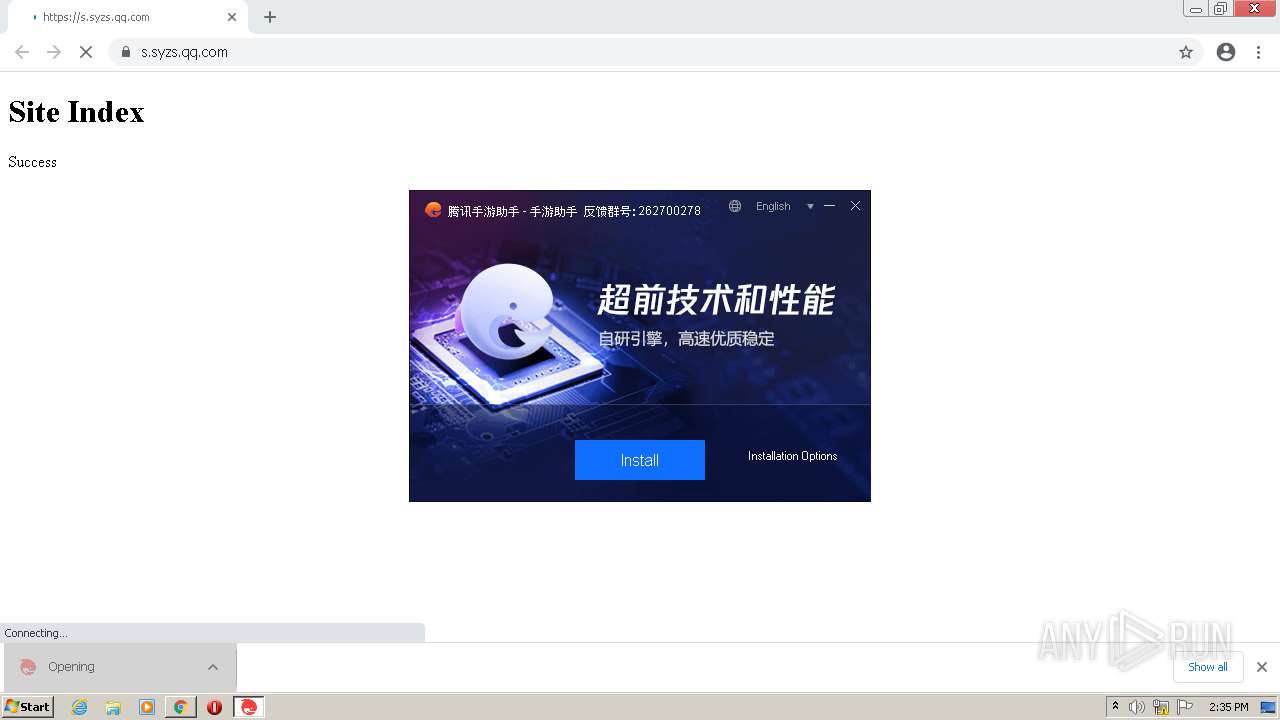
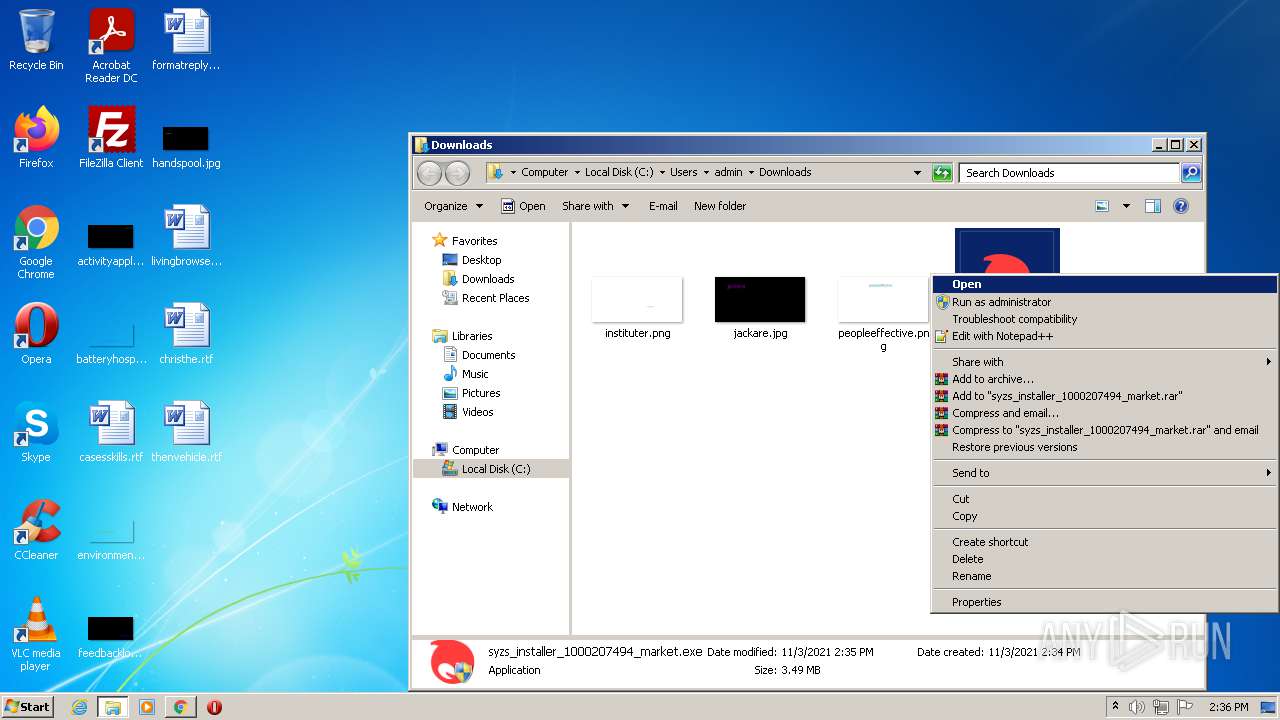
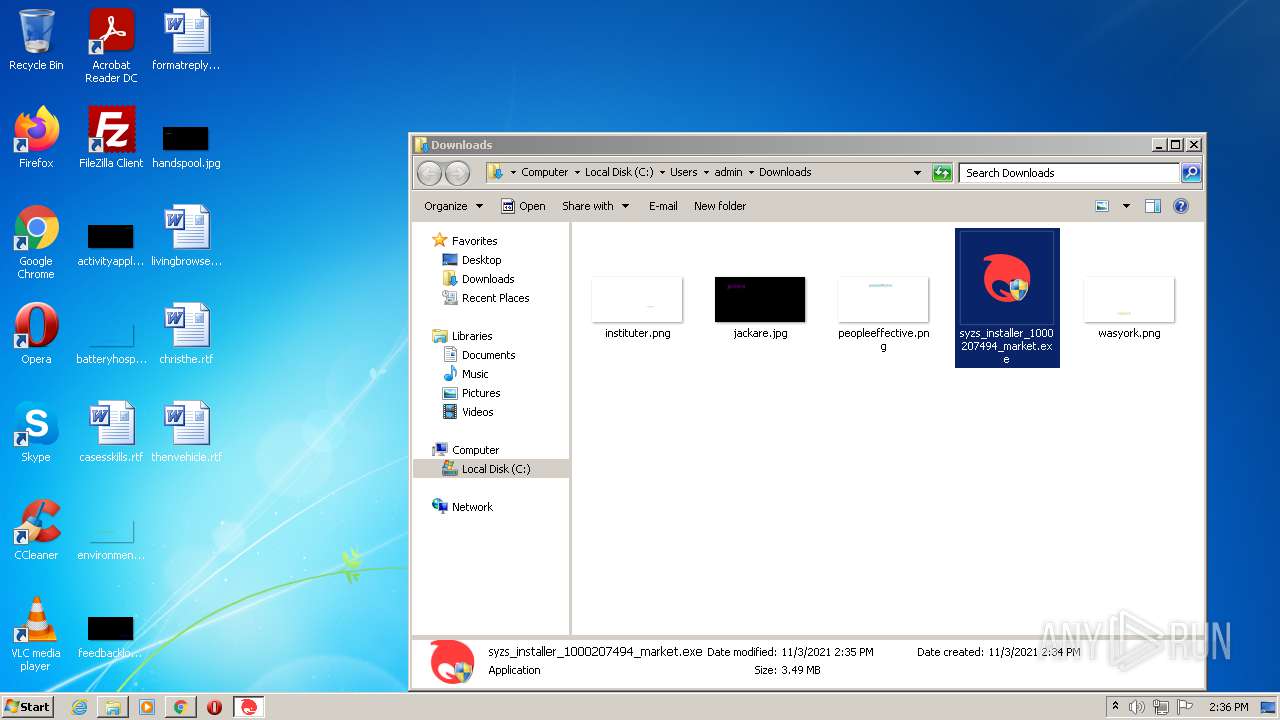
Application was dropped or rewritten from another process
- syzs_installer_1000207494_market.exe (PID: 3412)
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 1796)
- syzs_installer_1000207494_market.exe (PID: 3404)
Drops executable file immediately after starts
- syzs_installer_1000207494_market.exe (PID: 3884)
- chrome.exe (PID: 1024)
Loads dropped or rewritten executable
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 3404)
- syzs_installer_1000207494_market.exe (PID: 1796)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3560)
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 3404)
- chrome.exe (PID: 1024)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 3560)
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 3404)
- chrome.exe (PID: 1024)
Reads the computer name
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 3404)
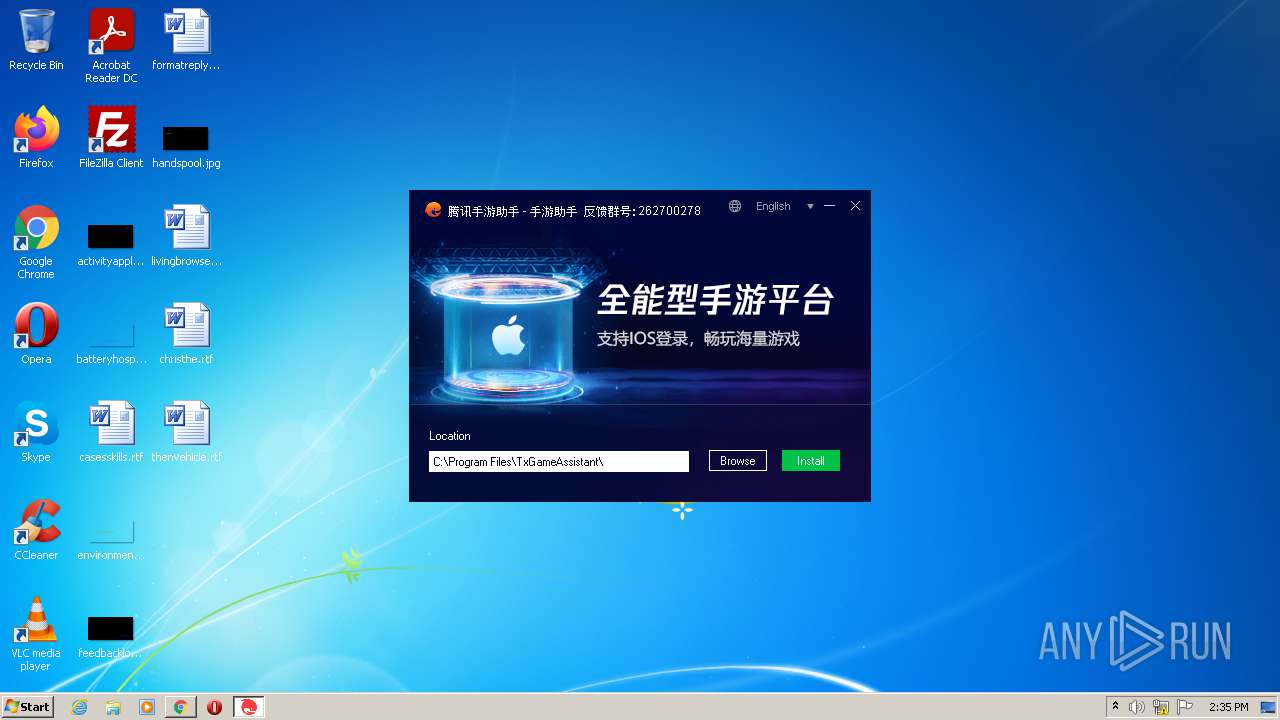
Creates a directory in Program Files
- syzs_installer_1000207494_market.exe (PID: 3884)
Checks supported languages
- syzs_installer_1000207494_market.exe (PID: 3884)
- syzs_installer_1000207494_market.exe (PID: 1796)
- syzs_installer_1000207494_market.exe (PID: 3404)
Creates files in the user directory
- syzs_installer_1000207494_market.exe (PID: 3884)
INFO
Reads the computer name
- chrome.exe (PID: 3560)
- chrome.exe (PID: 828)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 1904)
- chrome.exe (PID: 2892)
Reads the hosts file
- chrome.exe (PID: 3560)
- chrome.exe (PID: 828)
Checks supported languages
- chrome.exe (PID: 3560)
- chrome.exe (PID: 3692)
- chrome.exe (PID: 272)
- chrome.exe (PID: 828)
- chrome.exe (PID: 840)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 1612)
- chrome.exe (PID: 2320)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 2296)
- chrome.exe (PID: 3008)
- chrome.exe (PID: 3400)
- chrome.exe (PID: 3340)
- chrome.exe (PID: 3184)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2956)
- chrome.exe (PID: 2212)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 1904)
- chrome.exe (PID: 2892)
- chrome.exe (PID: 3628)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 1024)
- chrome.exe (PID: 3484)
Application launched itself
- chrome.exe (PID: 3560)
Reads settings of System Certificates
- chrome.exe (PID: 828)
- chrome.exe (PID: 3560)
- syzs_installer_1000207494_market.exe (PID: 3404)
Checks Windows Trust Settings
- chrome.exe (PID: 3560)
Reads the date of Windows installation
- chrome.exe (PID: 3128)
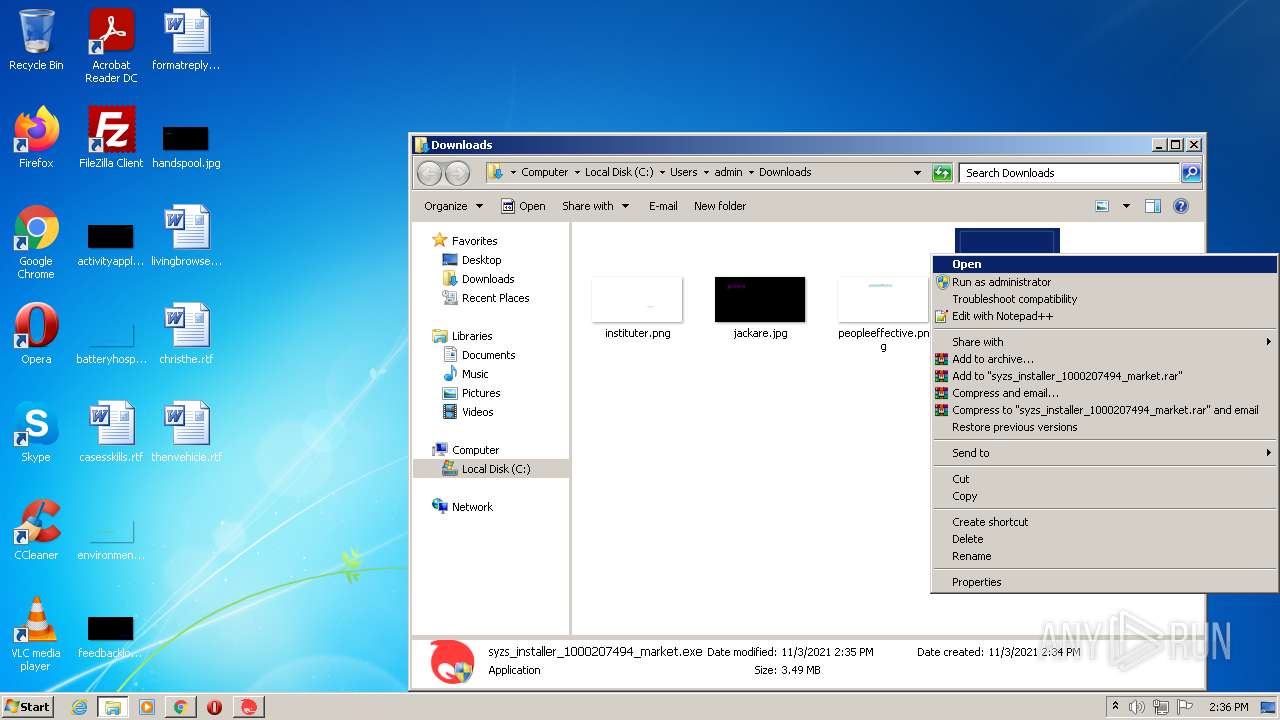
Manual execution by user
- syzs_installer_1000207494_market.exe (PID: 1796)
- syzs_installer_1000207494_market.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report


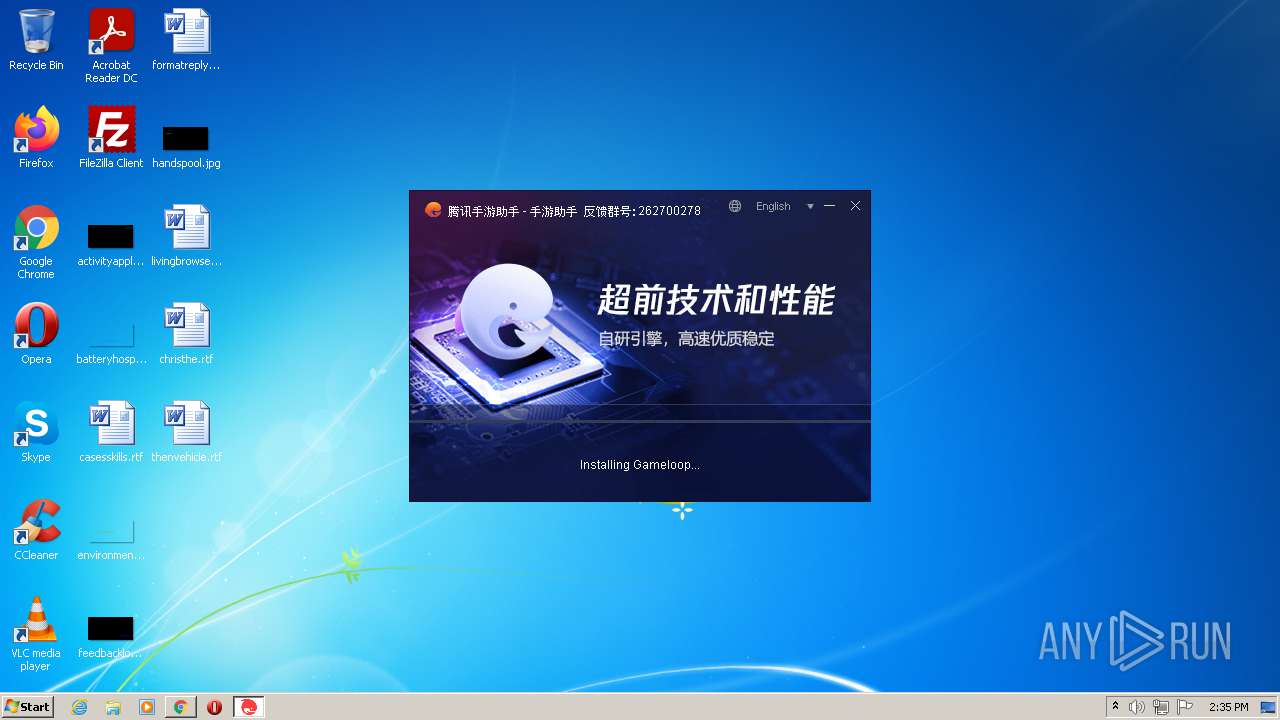
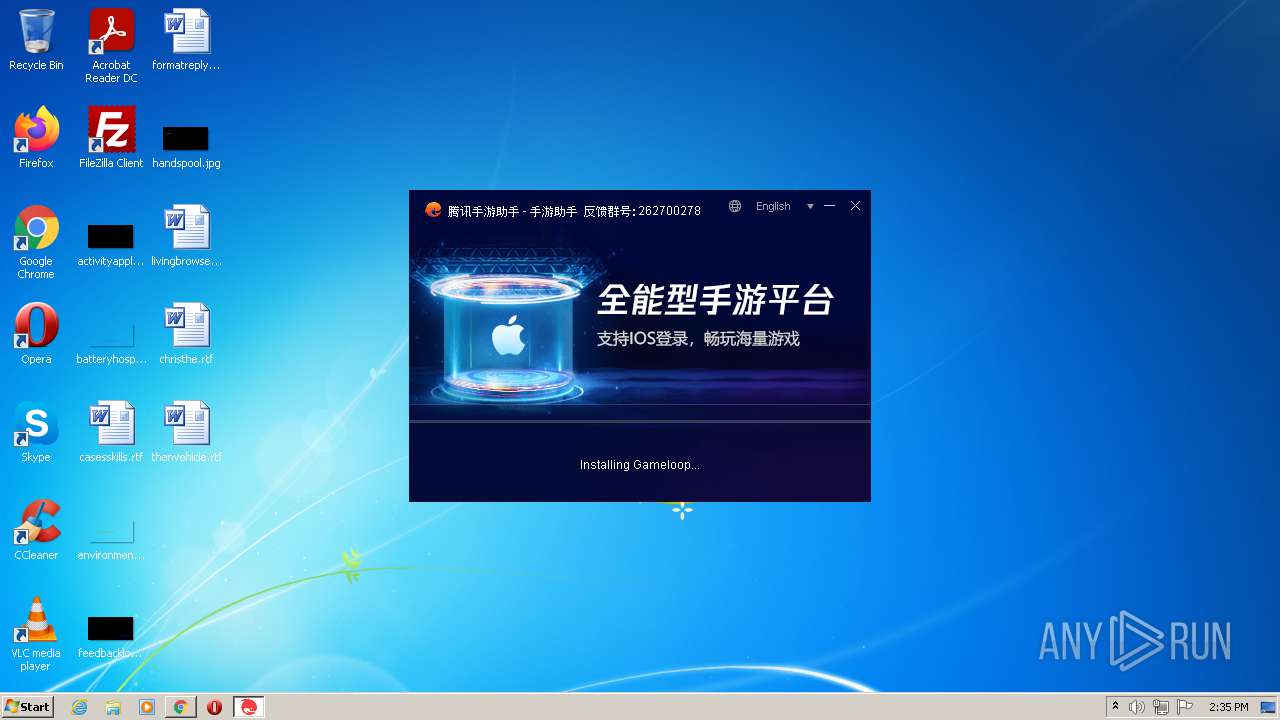

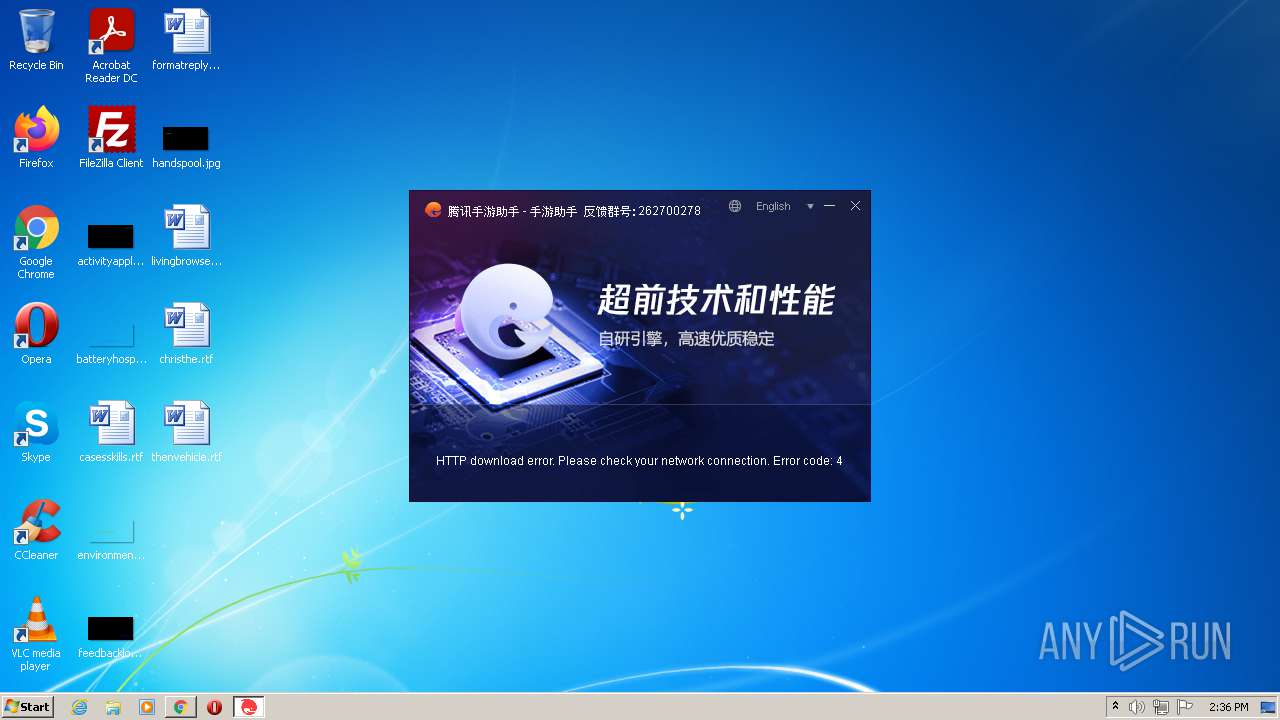
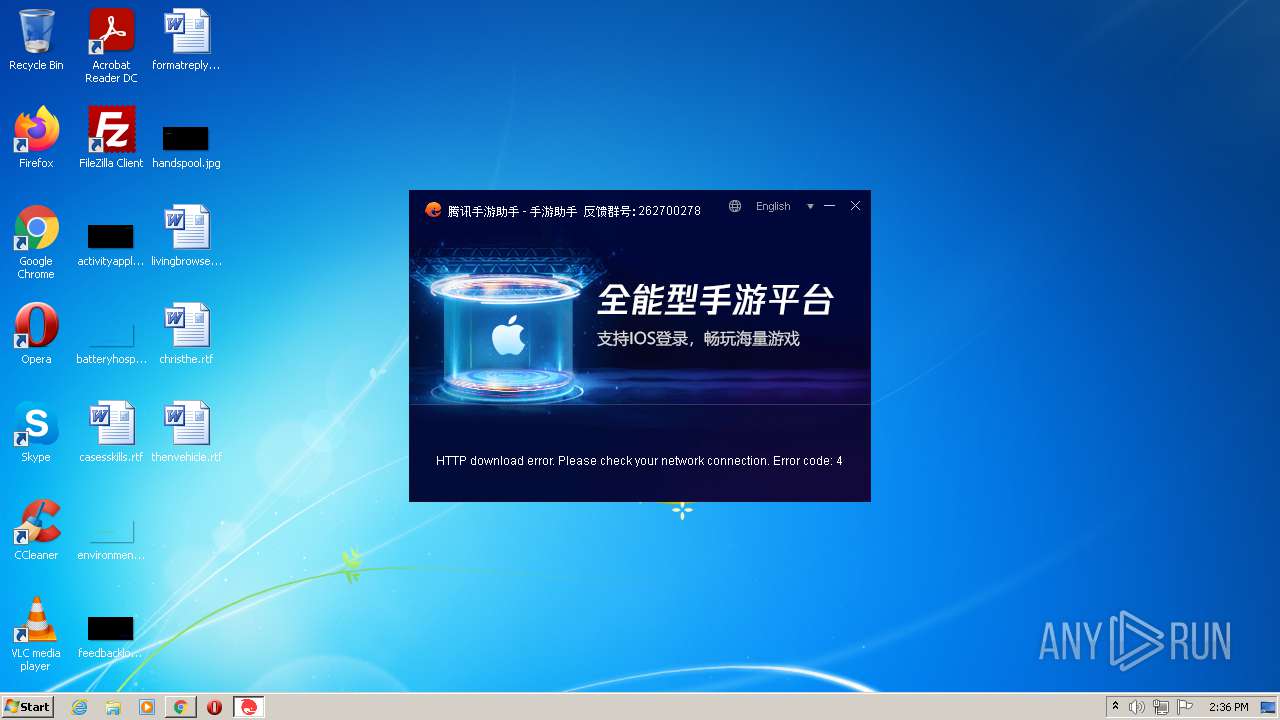

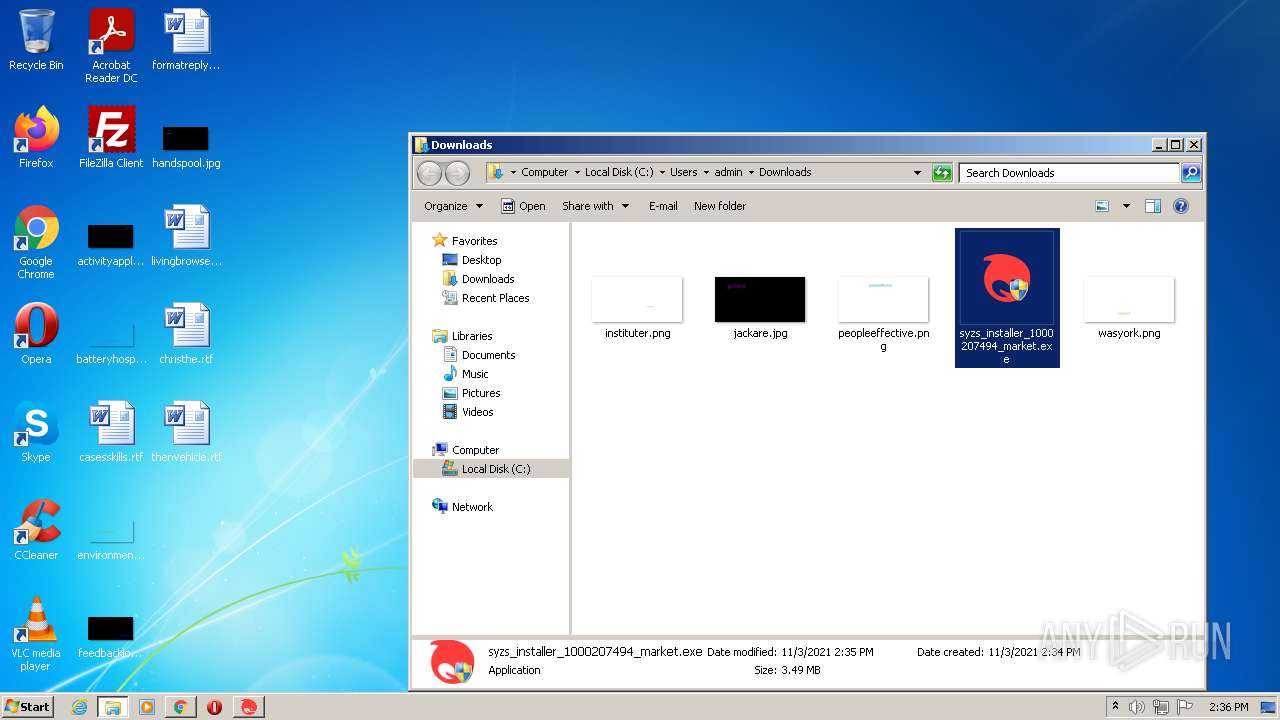

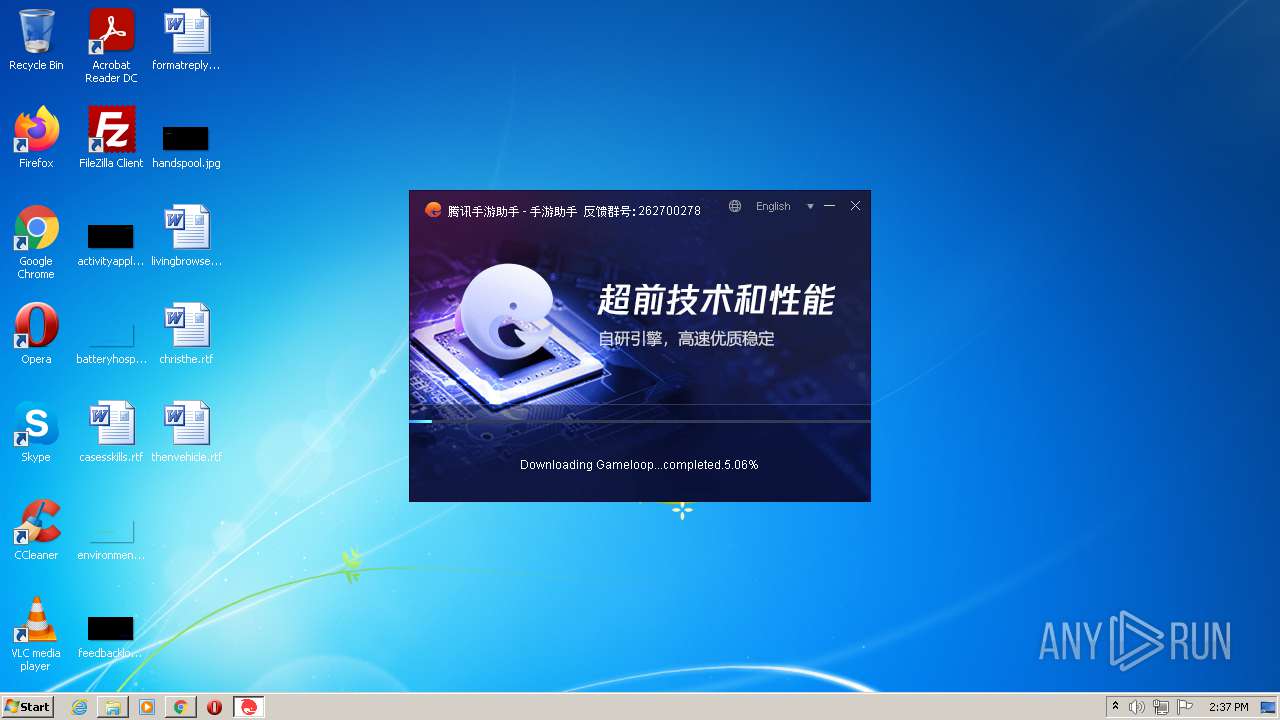
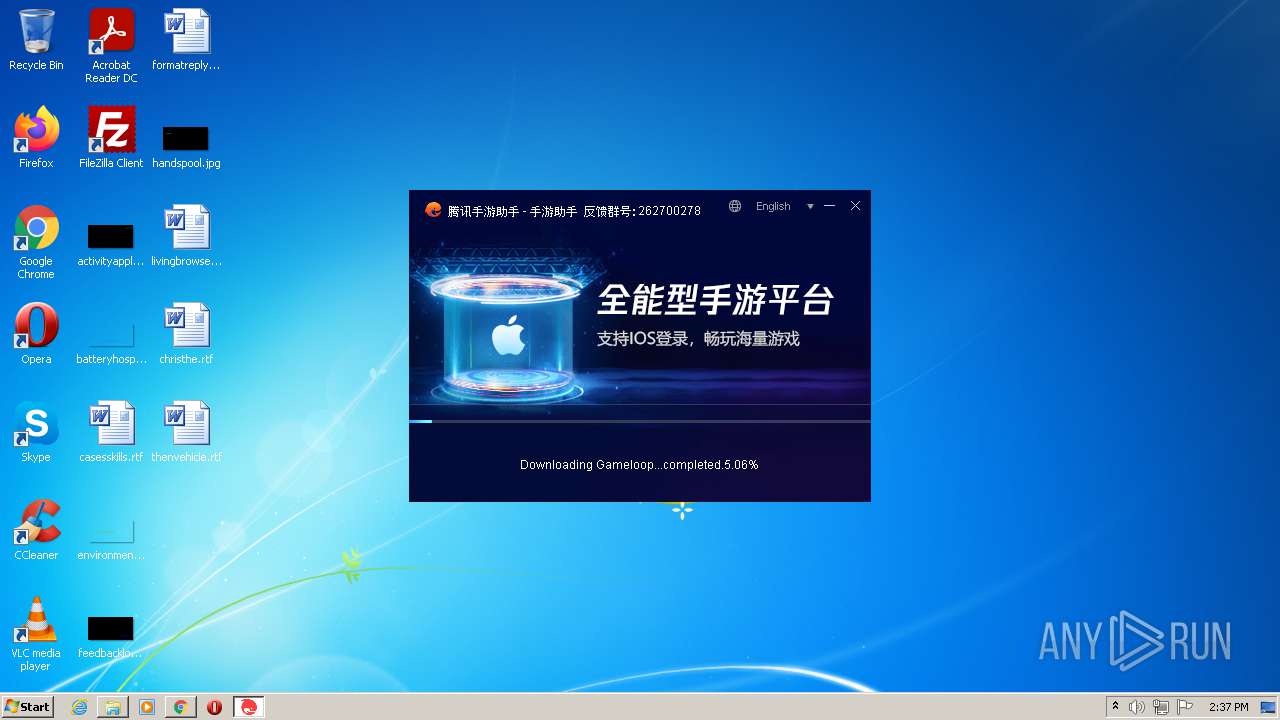
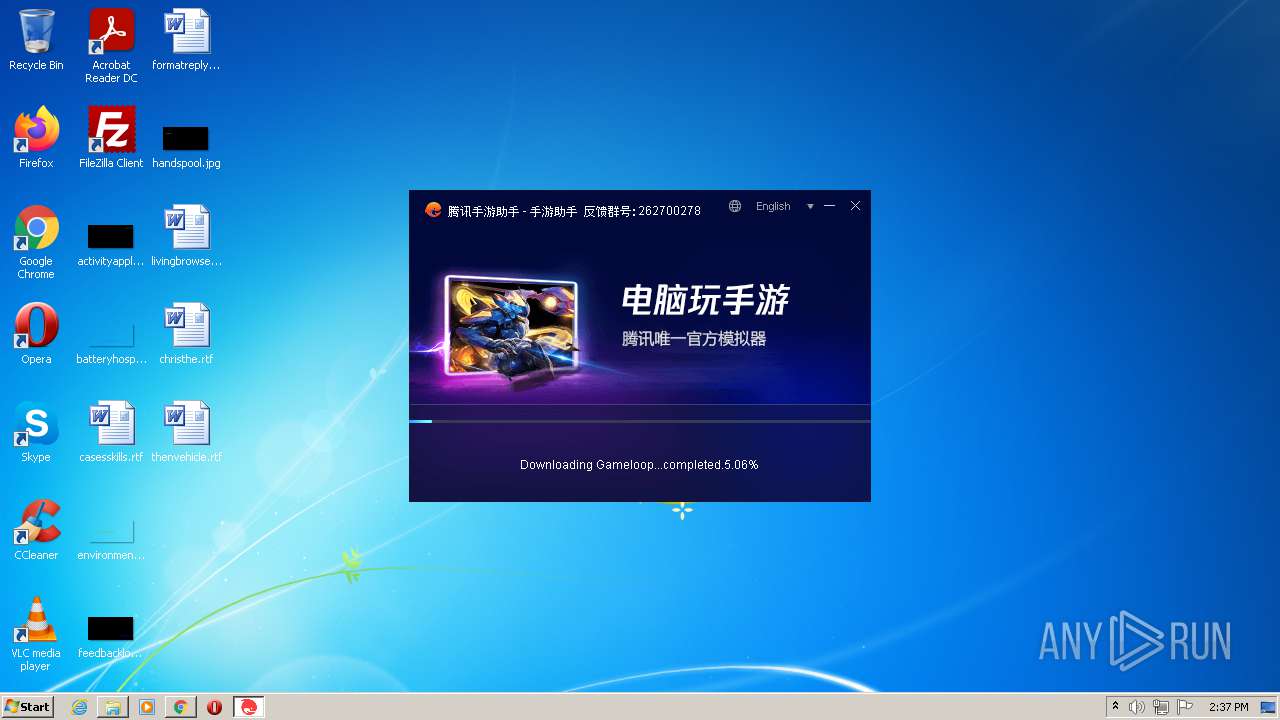
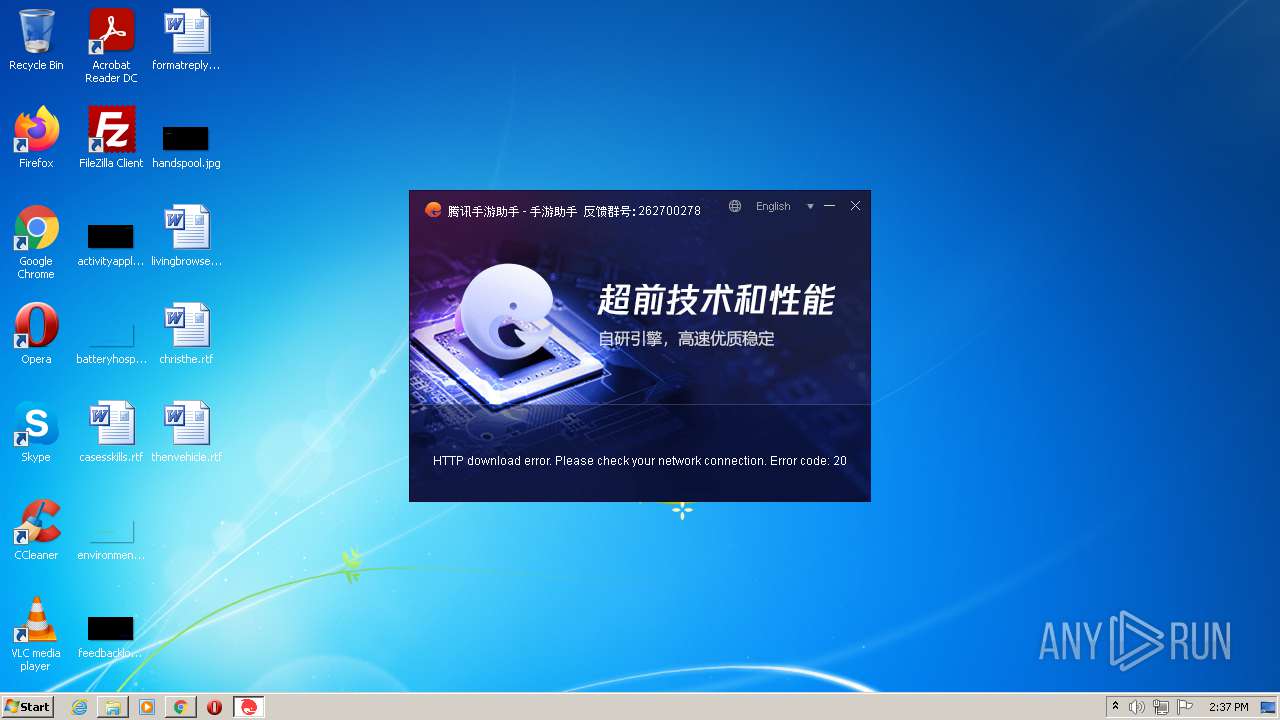
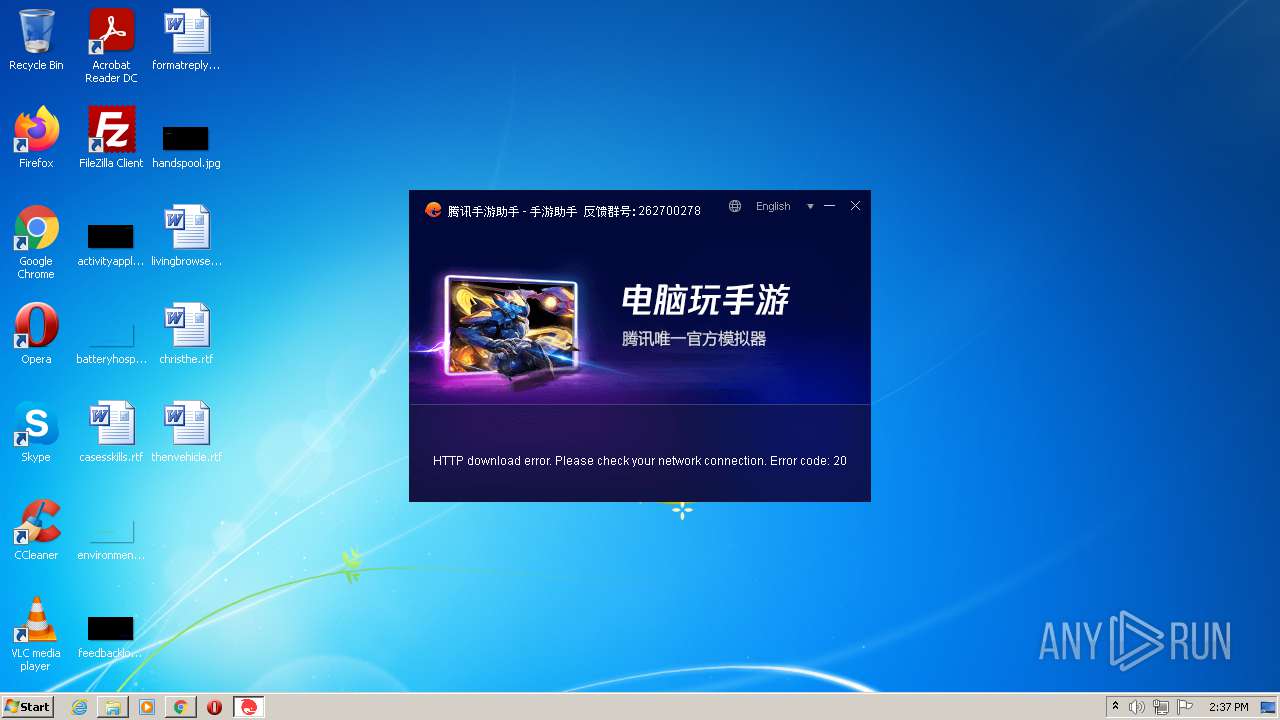
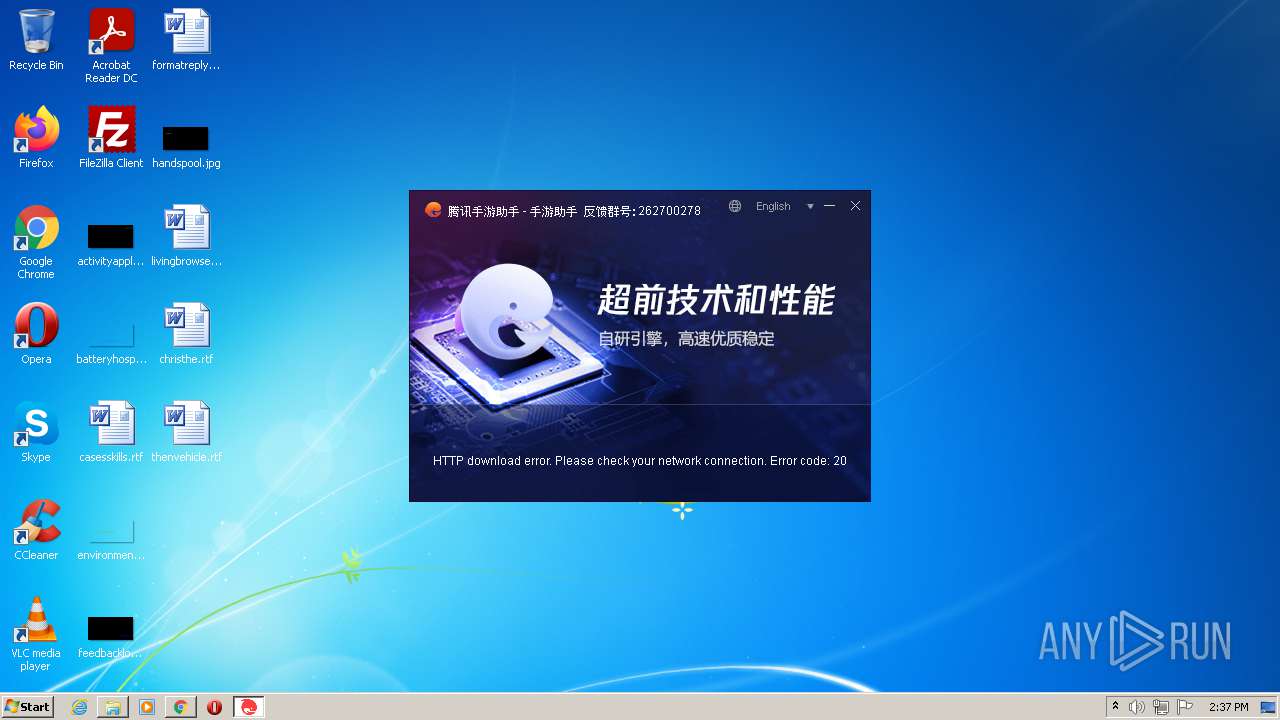
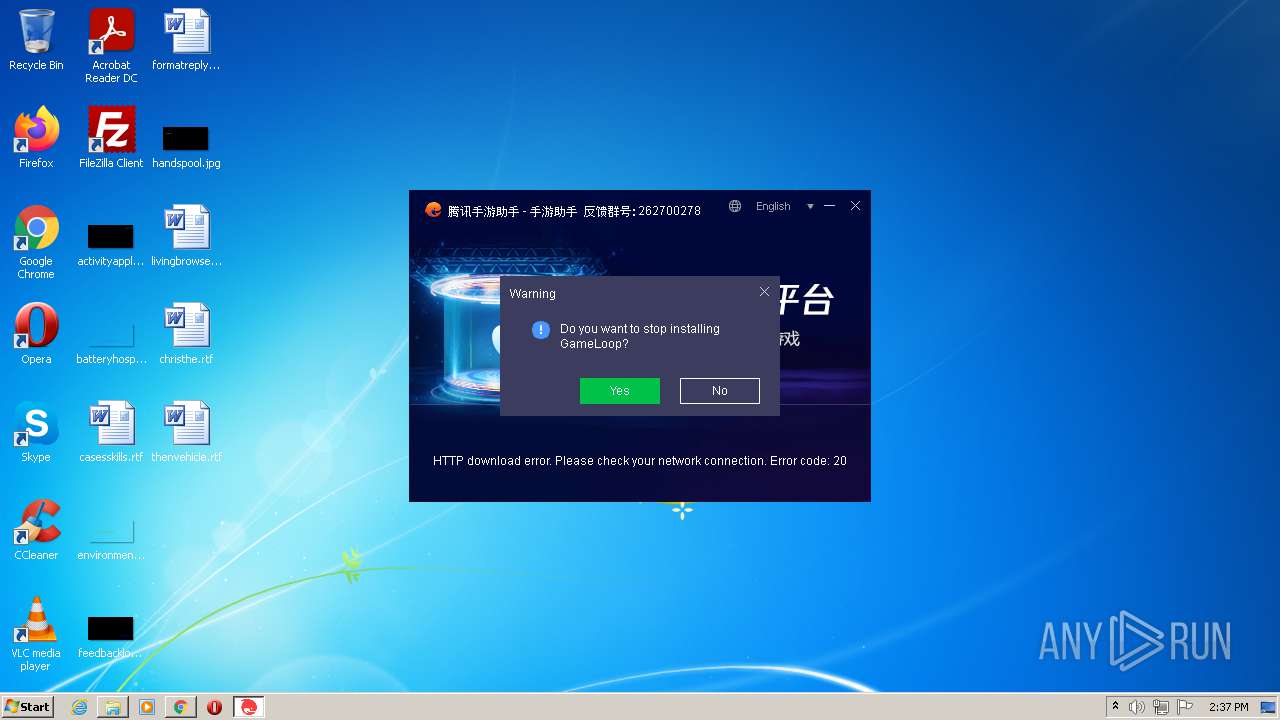

All screenshots are available in the full report
Total processes
75
Monitored processes
30
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://s.syzs.qq.com/k_pack_up/5326/c12687841/syzs_installer_1000207494_market.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 3692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6e6cd988,0x6e6cd998,0x6e6cd9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1248 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 86.0.4240.198 | ||||
| 840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1856 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1872 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2180 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1112 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 86.0.4240.198 | ||||
| 1612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2880 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
| 4080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --field-trial-handle=1032,1346360584050886501,16353222444707305984,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=icon_reader --mojo-platform-channel-handle=2900 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 | ||||
Total events
15 106
Read events
14 916
Write events
0
Delete events
0
Modification events
Executable files
6
Suspicious files
32
Text files
114
Unknown types
2
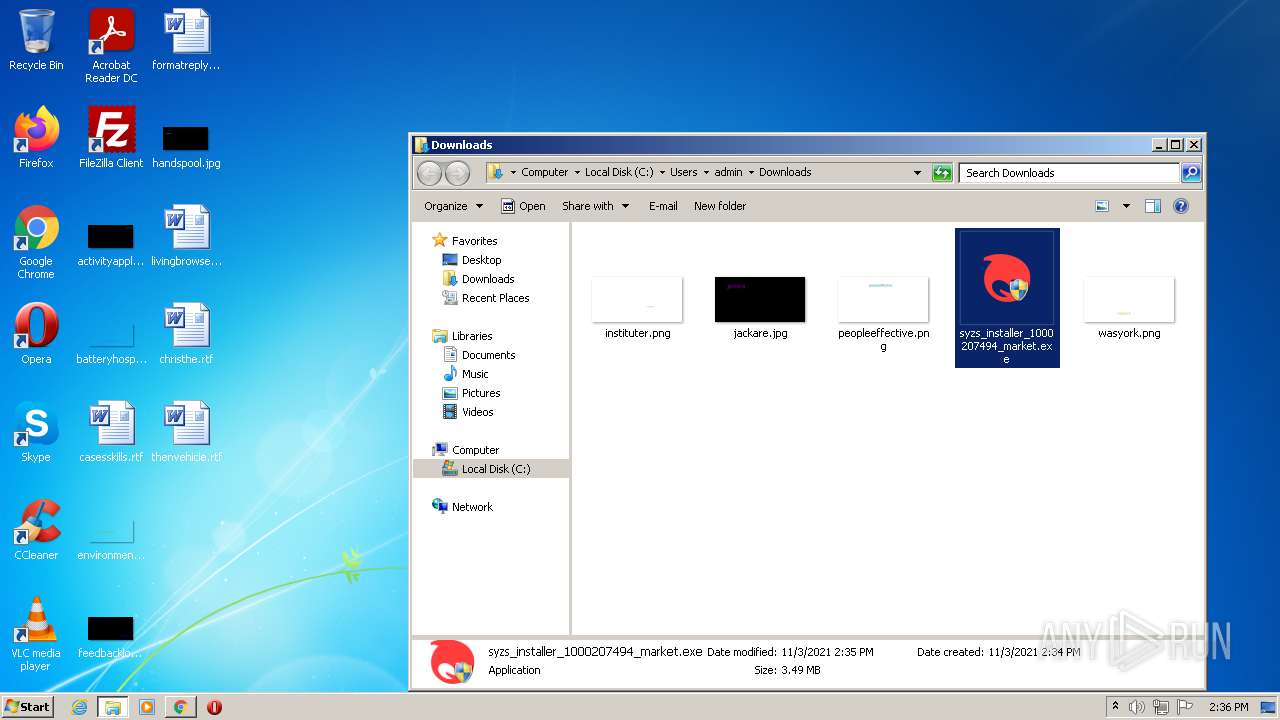
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61829E06-DE8.pma | — | |
MD5:— | SHA256:— | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:6E82888A5666205649ABA0BD62EC5D11 | SHA256:C54B2A11E788736264BA58994AAD2F1C75BA64117478BD5E0793D1485D3D10E3 | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\76b6f7d8-e1d9-4a05-893b-134830dab38a.tmp | text | |
MD5:6E82888A5666205649ABA0BD62EC5D11 | SHA256:C54B2A11E788736264BA58994AAD2F1C75BA64117478BD5E0793D1485D3D10E3 | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFef96f.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFef95f.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3692 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 3560 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFefa98.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
63
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
860 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 10.9 Kb | whitelisted |
3404 | syzs_installer_1000207494_market.exe | GET | — | 203.205.251.65:80 | http://dldir1.qq.com/syzs/syzs_cms/65d179233189e9c0da6ca76e4def320c.exe | CN | — | — | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 10.9 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 178 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 21.7 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 88.8 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 44.0 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 479 Kb | whitelisted |
860 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 358 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
828 | chrome.exe | 142.250.186.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
828 | chrome.exe | 142.250.186.77:443 | accounts.google.com | Google Inc. | US | suspicious |
828 | chrome.exe | 142.250.185.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
828 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
828 | chrome.exe | 101.33.11.110:443 | s.syzs.qq.com | — | CN | unknown |
828 | chrome.exe | 142.250.186.34:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
828 | chrome.exe | 142.250.185.66:443 | adservice.google.com | Google Inc. | US | whitelisted |
828 | chrome.exe | 142.250.185.130:443 | googleads.g.doubleclick.net | Google Inc. | US | suspicious |
— | — | 142.250.181.226:443 | partner.googleadservices.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
s.syzs.qq.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
partner.googleadservices.com |
| whitelisted |
adservice.google.dk |
| whitelisted |
adservice.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
3884 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
3404 | syzs_installer_1000207494_market.exe | Generic Protocol Command Decode | SURICATA TLS error message encountered |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
syzs_installer_1000207494_market.exe | Standard VGA Graphics Adapter |
syzs_installer_1000207494_market.exe | Standard VGA Graphics Adapter |
syzs_installer_1000207494_market.exe | Standard VGA Graphics Adapter |